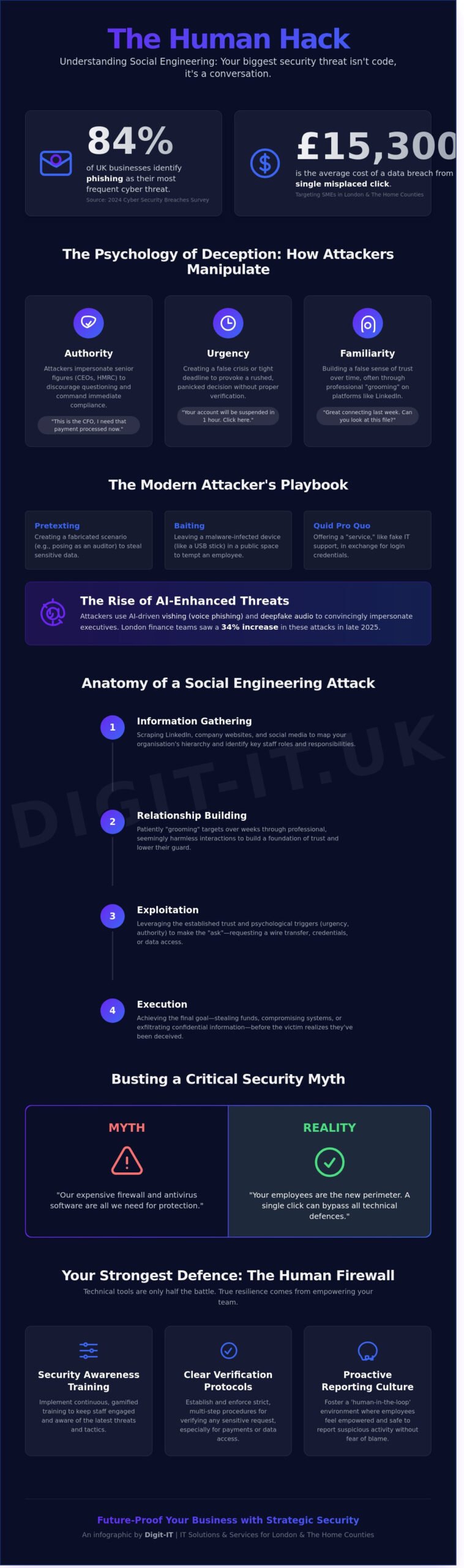
Did you know that 84% of UK businesses identified phishing as their most frequent threat last year, according to the 2024 Cyber Security Breaches Survey? While you have likely invested in robust firewalls, the most sophisticated threat to your London or Hertfordshire business isn’t a line of code; it is a conversation. Understanding social engineering in security is now the most critical step in your defensive strategy. You probably worry that a single misplaced click by a well-meaning staff member could lead to a £15,300 average cost for a data breach. It is a valid concern because technical tools are only as effective as the people who operate them.
We are here to help you build lasting resilience against these “human hacks” targeting SMEs across Buckinghamshire and the Home Counties. This guide moves past confusing jargon to show you exactly how these psychological tactics work in a local context. You will learn to identify the most common regional threats and discover how to train your team effectively. We will provide a proactive plan to ensure your business remains secure and future-proofed against evolving digital fraud, giving you the peace of mind to focus on your growth.
Key Takeaways
- Uncover why psychological manipulation has become the ‘path of least resistance’ for hackers targeting SMEs across London and the Home Counties.
- Identify the sophisticated psychological triggers-such as urgency and authority-used to groom victims through increasingly professional interactions.
- Challenge the myths surrounding cyber-resilience, including the dangerous assumption that firewalls alone protect against social engineering in security.
- Discover how to build a robust ‘human firewall’ by implementing gamified security awareness training and clear verification protocols for your staff.
- Learn how a proactive, ‘human-in-the-loop’ threat detection strategy provides the peace of mind needed to future-proof your business operations.
What is Social Engineering in Security and Why Does it Target SMEs?
Cybersecurity is no longer just a battle of code and encryption. As we move through 2026, hackers have pivoted away from brute-force attacks on firewalls, choosing instead to exploit the most vulnerable element in any organisation: the human mind. Social engineering (security) is the psychological manipulation of individuals to trick them into divulging confidential information or performing actions that compromise safety. It’s the path of least resistance because a single misplaced click can bypass a £100,000 security infrastructure in seconds.
While technical hacking focuses on finding flaws in software, social engineering in security targets the cognitive biases we all share. Attackers are currently leveraging AI-driven vishing (voice phishing) and deepfake audio to impersonate senior executives. In late 2025, London finance teams reported a 34% increase in fraudulent payment requests initiated by “clone” voices of managing directors. These attacks don’t require complex malware; they only require a convincing story and a moment of employee distraction to succeed.
The “Human Hack” Explained
Think of this approach as hacking the person rather than the machine. A common tactic is pretexting, where a criminal creates a fabricated scenario to steal data. For instance, an attacker might call a junior clerk pretending to be an external auditor who’s missing a specific VAT filing for the current quarter. By the time the clerk realises the error, the attacker has already secured access to the firm’s internal ledger. Social engineering is the art of exploiting human trust to bypass digital defences.
Why Hertfordshire and London Businesses are Prime Targets
The high density of professional services in St Albans and Watford makes Hertfordshire a goldmine for data harvesting. Criminals use LinkedIn to map out the hierarchy of a firm, identifying exactly who handles the accounts or manages the IT contracts. They capitalise on the 24/7 urgency culture of the London business scene, where the pressure to respond quickly often overrides the instinct to verify a request.
Statistics from the first quarter of 2026 show that 62% of SMEs in the Home Counties have been targeted by at least one sophisticated impersonation attempt. This proves that local presence is no shield against global threats, especially when attackers can mimic the professional tone of a local partner. Small businesses often lack the dedicated security training found in larger corporations, making them the ideal testing ground for new, AI-enhanced social engineering tactics.
The Psychology of Deception: How Attackers Organise Scams
Cybercriminals rarely start with a brute-force attack on your firewall. Instead, they target the most vulnerable part of your business: human psychology. By weaponising traits like trust and helpfulness, they bypass technical controls entirely. Most successful breaches rely on three primary triggers. Authority involves impersonating a senior executive or a government body like HMRC to discourage questioning. Urgency creates a false crisis, such as a “pending legal action,” to force a rushed decision. Finally, Reciprocity uses a small “favour” or gift to make the victim feel indebted.
Modern attackers are patient. They often “groom” victims over several weeks through professional interactions on LinkedIn or WhatsApp. This process builds a false sense of security before the trap is sprung. Within office environments, “Baiting” remains a potent threat. An attacker might leave a branded USB stick in a communal area or offer a “free” software tool that contains a hidden payload. Similarly, “Quid Pro Quo” scams involve an attacker posing as IT support, offering to “fix” a non-existent technical issue in exchange for login credentials. Research from UK Finance showed that £1.2 billion was stolen through fraud in 2022, proving that these psychological tactics are incredibly lucrative. Understanding the Dangers of Social Engineering is the first step in protecting your team from these sophisticated manipulation techniques.
The Four Stages of a Social Engineering Attack
A structured attack follows a methodical path. First, Information Gathering involves scraping LinkedIn and company websites to identify staff roles. Second, Relationship Building starts with an “innocent” contact, perhaps a request for a quote or a shared industry interest. Third, Exploitation occurs when the attacker makes their move, asking for a bank transfer or a password reset. Finally, Execution/Exit involves the attacker closing the loop and deleting their digital footprint before the victim realises they’ve been compromised.
Common Tactics: Phishing, Vishing, and Smishing
Attackers use a “multi-channel” approach to increase their success rates. Phishing (email) is often the entry point, but it’s frequently paired with Vishing (voice calls) and Smishing (SMS). By 2026, we expect to see a surge in AI-generated voice clones. Imagine a finance manager receiving a WhatsApp message about an urgent invoice, followed immediately by a phone call from their “CFO” confirming the request. The voice is identical, the tone is perfect, and the pressure is high. This level of social engineering in security requires a proactive strategy. You can optimise your human firewall by training staff to verify every out-of-character request through a secondary, trusted channel.
Myth-Busting: 5 Misconceptions About Social Engineering
Believing your business is safe because you’ve invested in high-end hardware is a dangerous oversight. Cybercriminals don’t always look for a digital back door; they often walk through the front entrance using credentials handed to them by an employee. To build true resilience, you must first dismantle these five common myths about social engineering in security.
- Myth 1: “Our Firewall and Antivirus Make Us Immune.” Technology protects your perimeter, but it can’t vet the intent of a person using valid login details.
- Myth 2: “Social Engineering is Always a Poorly Written Email.” Modern attacks are sophisticated. AI tools now allow criminals to craft perfect, error-free communications that mimic your bank or a trusted supplier.
- Myth 3: “Only Large Corporations in London are Targeted.” Geography offers no protection. Small firms in the Home Counties are often viewed as softer targets with fewer defences.
- Myth 4: “My Staff Would Never Fall for a Scam.” Even the most loyal, diligent employees can be manipulated during a high-pressure moment or a busy Friday afternoon.
- Myth 5: “MFA (Multi-Factor Authentication) Solves Everything.” While essential, MFA is not a total cure. Attackers have developed specific tactics to bypass these prompts.
Why Technology Alone is Not a Silver Bullet
A firewall is designed to block unauthorised traffic. However, when an attacker uses a stolen password, they appear as a legitimate user. The system doesn’t see a breach; it sees a standard login. This is why understanding What is Social Engineering? is vital for every business leader. It shifts the focus from purely technical fixes to human-centric strategy.
We’ve seen a rise in “MFA fatigue” attacks. This involves an attacker spamming a user’s phone with login approval requests. Eventually, the distracted employee clicks “approve” just to stop the persistent notifications, unwittingly granting the hacker full access. Similarly, security software cannot intervene when a staff member receives a phone call from a “fake” IT support agent and voluntarily provides remote access to their workstation.
The Reality for SMEs in Buckinghamshire and Beyond
The Cyber Security Breaches Survey 2023 revealed that 32% of UK businesses identified a cyber attack in the previous 12 months. For small and medium enterprises (SMEs), these figures are often higher because they lack the dedicated security teams found in the City. Smaller firms in Buckinghamshire are frequently targeted because their training programmes are less frequent, making them “easy wins” for opportunistic hackers.
The impact of a breach extends far beyond the initial financial loss. In tight-knit business communities across Hertfordshire, reputation is everything. A data leak involving client information can destroy years of trust in hours. When sensitive data is compromised, it often ends up being sold on the dark web within 48 hours, making recovery even more challenging. Proactive social engineering in security measures ensure your business remains a reliable partner rather than a cautionary tale. We focus on future-proofing your organisation by bridging the gap between your digital tools and the people who use them every day.
Building a “Human Firewall” in Your Organisation
Technology acts as your shield, but your employees remain the final line of defence. Addressing social engineering in security requires more than just high-end software; it demands a cultural shift. According to the 2023 Verizon Data Breach Investigations Report, 74% of all breaches involve a human element. We focus on transforming your staff from a potential vulnerability into a proactive asset. By establishing clear verification protocols, you ensure that no single person can authorise a high-risk transaction without a secondary check. For instance, when a finance assistant receives an urgent email from a “Director” requesting a £10,000 payment to a new vendor, the protocol must require a verbal confirmation via a trusted phone number.
Resilience is built through a “Zero Trust” architecture within your managed IT infrastructure. This model operates on the principle of “never trust, always verify,” regardless of whether a request originates from inside or outside the network. In shared London office spaces, physical security is equally vital. Tailgating, where an unauthorised individual follows a staff member through a secure door, is a common tactic in high-traffic buildings in the City or Canary Wharf. Enforcing strict “no-swipe, no-entry” rules prevents physical intruders from gaining access to your internal hardware.
Practical Training Strategies for Staff
Effective training moves beyond ticking a compliance box. It focuses on genuine behavioural change. We recommend gamified security awareness programmes that reward staff for identifying risks. You can run simulated phishing tests to measure readiness, but it’s vital to do so without creating a culture of fear. If an employee clicks a simulated link, use it as a teaching moment rather than a disciplinary one. Training must include everyone from the receptionist to the CEO. A “no-blame” culture encourages staff to report suspicious activity immediately. If a team member reports a mistake within 15 minutes, your IT partner can often isolate the threat before it escalates into a full-scale breach.
Policy and Procedure: Your Best Defence
Strong policies provide the framework for social engineering in security management. A “double-check” rule for all bank detail changes is non-negotiable. If a supplier emails to say their accounts have changed, your team must verify this through a separate, established communication channel. Handling hardware requires similar rigour. We’ve seen cases where “lost” USB drives left in office lobbies were used to plant malware. Adopting the Cyber Essentials certification helps standardise these procedures. This UK government-backed scheme can reduce your organisation’s cyber risk by up to 80% by ensuring basic technical controls are in place. These structured policies ensure your business remains secure, even when human intuition fails.
Protect your team and your data by implementing a strategy that balances technical precision with human awareness. Secure your business today with a comprehensive security audit from our expert advisors.
Strategic Security: How Digit-IT Future-Proofs Your Business
Digit-IT delivers a proactive security posture for businesses across London. We don’t wait for a crisis to occur; we anticipate it. Our approach centres on 24/7 monitoring combined with a “Human-in-the-Loop” threat detection system. This hybrid model ensures that while AI flags anomalies, our expert analysts verify the intent behind the data. Because social engineering in security targets human psychology, we integrate comprehensive staff training into our standard IT support packages. Our physical presence in Hertfordshire allows us to provide rapid on-site response within 120 minutes for critical issues, ensuring your local operations remain resilient against evolving digital threats.
Managed Security vs. Traditional IT Support
The traditional “break-fix” model is a liability. It relies on reactive repairs that fail to stop sophisticated social engineering in security before they compromise your data. Strategic partnership is the only way to stay ahead. We conduct regular security audits and consultancy sessions to identify vulnerabilities in your workflows. A key part of our service involves optimising your Microsoft 365 environment. By implementing advanced “Safe Links,” “Safe Attachments,” and Conditional Access policies, we reduce the likelihood of a successful phishing attempt reaching your employees by up to 82% compared to default settings. We don’t just fix hardware; we build a digital fortress around your communication channels.
Peace of Mind for Business Owners
Digit-IT acts as your Trusted Advisor. We handle the technical intricacies so you can focus on growth. The ROI of prevention is undeniable. According to the Cyber Security Breaches Survey 2024, 70% of medium-sized UK businesses identified a breach in the last year. While a single successful social engineering breach cost UK small businesses an average of £11,000 in recovery and downtime in 2023, our managed service provides a predictable monthly cost that secures your bottom line. We function as an agile extension of your internal team, looking over the horizon for future risks. Our goal is to make IT an advantage, not a source of anxiety. We provide the composure you need to lead your company with confidence.
Take the first step toward total resilience. Book Your Free Cyber Security Health Check in London to identify your hidden risks and secure your infrastructure.
Future-Proof Your London or Hertfordshire Business Today
As we approach 2026, the digital landscape for SMEs demands more than just standard software. It requires a strategic shift in mindset. You’ve seen how modern attackers exploit human psychology to bypass even the most expensive technical barriers. Addressing social engineering in security isn’t just a technical checkbox; it’s a fundamental business necessity. By building a resilient human firewall and dismantling common myths about scam sophistication, you create a culture of vigilance that secures your long-term growth.
Digit-IT brings over 20 years of experience in UK IT support directly to your organisation. Our Cyber Essentials certified experts provide dedicated local support across London, Herts, and Bucks. We don’t just react to threats; we act as your strategic partner to ensure your infrastructure remains seamless and secure. Protecting your business continuity is what we do best.
Take the first step towards total digital peace of mind. Request a tailored Cyber Security Audit for your business and let’s ensure your team is prepared for the challenges of tomorrow. We’re here to help you build a safer, more resilient future.
Frequently Asked Questions
What is the most common form of social engineering for UK businesses?
Phishing remains the most prevalent threat, accounting for 84% of cyber attacks reported by UK businesses in the 2024 Cyber Security Breaches Survey. This common form of social engineering in security often involves deceptive emails designed to harvest credentials or deploy malware. By mimicking trusted organisations like HMRC or major banks, attackers exploit the psychological pressure of deadlines to bypass your technical defences.
How can I tell if an email is a social engineering attempt?
You can identify a social engineering attempt by scrutinising the sender’s address and checking for a sense of manufactured urgency. Look for subtle misspellings in the domain name, such as “digit-it.co” instead of the correct “.co.uk”, or generic greetings that fail to use your name. If an email demands an immediate financial transfer or asks for your password, it’s almost certainly a scam.
Does Cyber Essentials certification cover social engineering?
Cyber Essentials certification provides a foundational framework that mitigates social engineering risks by enforcing strict access controls and multi-factor authentication. While the scheme focuses on technical controls, the April 2023 update emphasises the importance of user awareness as part of a holistic defence strategy. Achieving this certification can reduce your organisation’s vulnerability to common internet-based threats by up to 80%.
What should I do if an employee falls for a social engineering scam?
You must immediately isolate the affected device from the network and reset all compromised credentials to prevent lateral movement. Report the incident to Action Fraud and your IT partner within 60 minutes to minimise potential data loss. We recommend a “no-blame” culture where staff feel confident reporting mistakes, as early detection is the most effective way to protect your business continuity.
Can AI help prevent social engineering attacks in 2026?
AI will be a critical tool for detecting sophisticated deepfake and voice-cloning attacks by 2026. Predictive algorithms will analyse communication patterns in real-time to flag anomalies that human eyes might miss. This proactive approach to social engineering in security ensures your team has a digital safety net that evolves as quickly as the threats themselves, allowing you to focus on growth.
Is social engineering more common in remote or office-based teams?
Remote teams are 47% more likely to fall for social engineering scams because they lack the immediate ability to verify requests with colleagues in person. The physical distance creates a “verification gap” that attackers exploit through platforms like Slack or Microsoft Teams. Implementing a formal verification protocol for out-of-band requests is essential for maintaining resilience in a hybrid or remote work environment.
How often should we conduct security awareness training?
You should conduct security awareness training at least every 90 days to ensure defensive habits remain sharp. Research from 2023 suggests that employee retention of security protocols drops significantly after four months without reinforcement. Short, monthly “micro-learning” sessions are often more effective than a single annual workshop for building a genuine culture of vigilance across your entire workforce.
Are Macs more resistant to social engineering than Windows PCs?
Macs aren’t more resistant to social engineering because these attacks target human psychology rather than operating system vulnerabilities. While macOS has robust built-in security features, a user can still be tricked into giving away their Apple ID or banking details on a fraudulent phishing site. Your security strategy must focus on the individual user’s decision-making process, regardless of the hardware they use to access your systems.