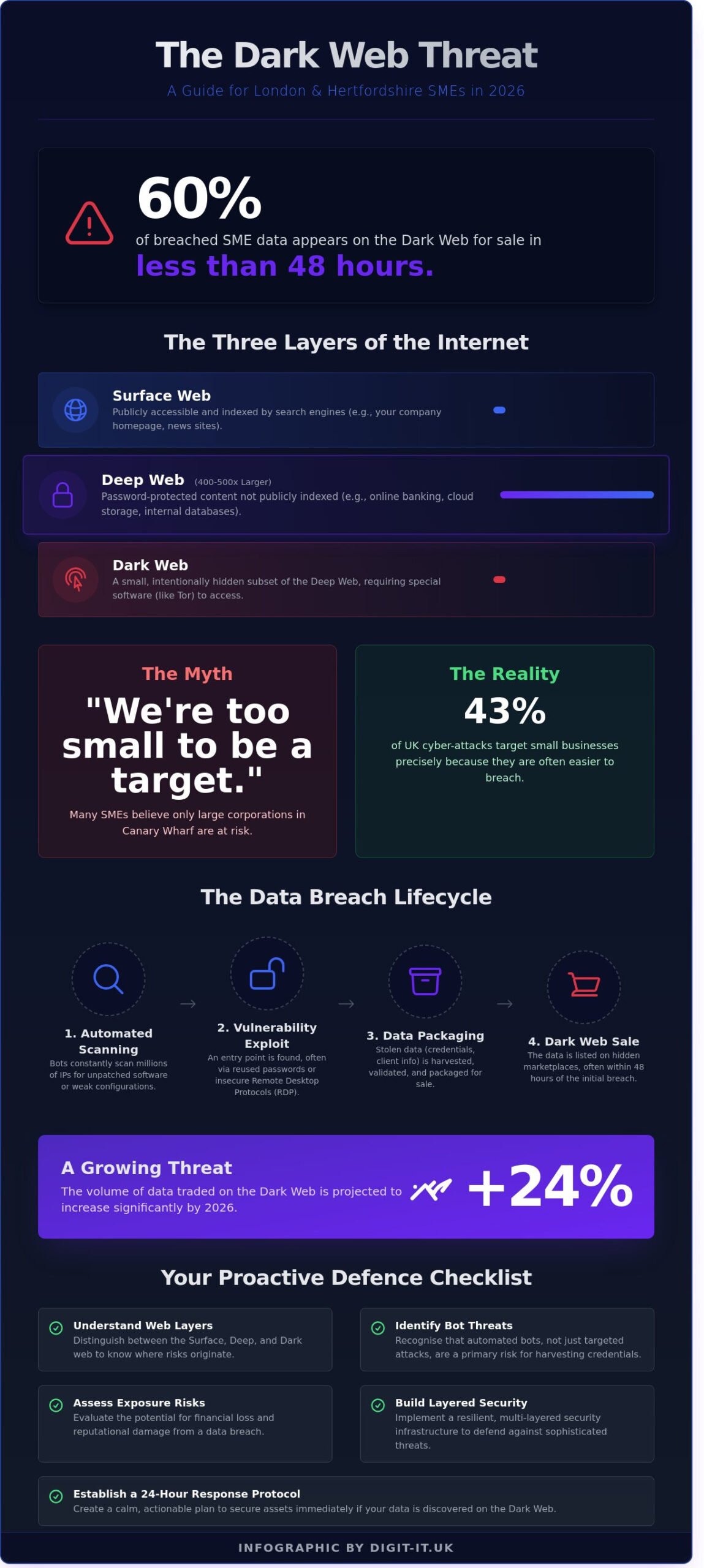
By the start of 2025, 60% of small businesses in London that suffered a security breach found their sensitive client data listed for sale on the dark web in less than 48 hours. It’s a sobering figure that highlights just how quickly local firms can lose control of their digital assets. You’ve likely invested in basic security and worked hard to meet UK GDPR standards, yet the fear of a hidden threat damaging your hard-earned reputation remains a constant weight on your shoulders.
We understand that the technical jargon surrounding cybercrime often makes the problem feel insurmountable. This guide is designed to change that by providing a clear, jargon-free look at the real risks facing your Hertfordshire business in 2026. You’ll discover what the dark web actually represents for your company and learn the proactive steps necessary to secure your data integrity. We’ll conclude with an actionable checklist to ensure your infrastructure remains resilient, giving you the peace of mind to focus on growth rather than digital vulnerabilities.
Key Takeaways
- Understand the distinction between the surface web and the hidden layers used by cybercriminals to target UK businesses.
- Identify how automated bots scan for vulnerabilities to harvest credentials from SMEs across London and the Home Counties.
- Assess the strategic risks of data exposure, from immediate financial loss to the lasting impact on your professional reputation.
- Learn to build a resilient, layered security infrastructure that future-proofs your organisation against sophisticated digital threats.
- Establish a calm, 24-hour response protocol to secure your assets should your data ever appear on the dark web.
Understanding the Dark Web: A Guide for London and Hertfordshire Businesses
The dark web isn’t just a plot device for a detective series; it’s a tangible segment of the internet that requires specific tools to access. For a business owner in St Albans or a director in the City of London, clarity on this topic provides the foundation for digital resilience. You can’t protect what you don’t understand. Essentially, the dark web is a collection of websites that exist on an encrypted network. You won’t find these sites on Google or Bing. Instead, users must employ specific software, most commonly The Onion Router (Tor), to reach them. This software anonymises the user’s IP address by bouncing it through several servers globally.
While the name sounds inherently sinister, the technology itself is neutral. It’s a tool for privacy. Journalists, whistleblowers, and activists use it to communicate without fear of state surveillance. However, that same anonymity attracts cyber criminals who trade in stolen data. Understanding the Dark Web involves recognising that while the platform isn’t illegal, the marketplaces hosted there often facilitate the sale of stolen credentials and sensitive business information. By 2026, the volume of data traded in these hidden corners is projected to increase by 24% compared to 2024 figures, making it a critical area for proactive monitoring.
The Three Layers of the Internet
To secure your operations, you must distinguish between the different tiers of digital space. Each layer serves a specific purpose for your business continuity.
- Surface Web: This is the publicly accessible portion of the internet. It includes your business homepage, news sites like the BBC, and anything indexed by search engines.
- Deep Web: This layer contains password-protected data. Your online banking portals, private cloud storage, and internal payroll databases live here. It’s roughly 400 to 500 times larger than the surface web.
- Dark Web: A small, intentionally hidden subset of the deep web. It uses “hidden services” with .onion domains that aren’t accessible via standard browsers like Chrome or Safari.
Common Myths vs Reality for UK Business Owners
A frequent misconception among Hertfordshire SMEs is the belief that they’re “too small” to be a target. Many owners assume that only the massive financial institutions in Canary Wharf face threats from the dark web. The reality is quite different. Smaller firms often have less robust security protocols, making them an easier “entry point” for criminals. In 2025, 43% of UK cyber attacks targeted small businesses because their data is often easier to harvest and sell on hidden marketplaces. Protecting your firm means moving beyond reactive measures and adopting a proactive managed infrastructure that monitors for leaked credentials before they can be exploited. This approach ensures your business remains agile and secure in an increasingly complex digital environment.
How Your Business Data Ends Up in the Digital Underworld
Your company data doesn’t simply vanish after a breach; it follows a structured, commercial path from your local network to a listing on the dark web. Criminals don’t always target your business specifically. Instead, they use automated bots to scan millions of IP addresses across London and Hertfordshire every hour, looking for unpatched software or misconfigured servers. Once these bots identify a weakness, the data breach lifecycle begins. This process moves rapidly from initial theft and validation of data to its eventual packaging and sale on illicit forums. By 2026, the speed of this cycle has increased, with stolen credentials often appearing for sale within 48 hours of the initial compromise.
A significant risk for many firms is the habit of reusing passwords across personal and professional accounts. If an employee’s personal social media account is compromised, attackers will immediately try those same credentials against your corporate VPN or email systems. Understanding these dark web threats for businesses is the first step in building a proactive defence strategy that protects your reputation and your bottom line.
Vulnerabilities for South East SMEs
Poorly secured Remote Desktop Protocols (RDP) remain a primary entry point for unauthorised access in the South East. Many businesses in Hertfordshire opened these ports to facilitate remote work without implementing proper multi-factor authentication, essentially leaving a digital back door unlocked. There’s also a direct connection between social engineering in security and the data found on the dark web. Phishing remains the most effective way to harvest the high-level credentials that criminals crave. Furthermore, “shadow IT”—the use of unauthorised software or personal cloud storage by staff—creates massive security holes that your IT team can’t protect because they don’t know they exist.
The Marketplace for Stolen Credentials
Initial Access Brokers are specialist threat actors who gain entry to your network and then sell that verified access to the highest bidder on underground forums. These brokers don’t usually carry out the final attack; they provide the “keys to the kingdom” for ransomware groups. Your data is often bundled into “combo lists,” which contain thousands of email addresses and passwords sold in bulk for as little as £20. Corporate credit card data is even more lucrative, with valid UK business card details fetching between £50 and £120 depending on the credit limit. To ensure your systems aren’t the next listing, you can explore our proactive security services designed to identify and close these gaps before they’re exploited.
The Risks: Why the Dark Web is a Threat to Greater London SMEs in 2026
For a business in Hertfordshire or the City, the dark web isn’t just a distant concept; it’s a marketplace where your company’s survival is auctioned to the highest bidder. The financial impact of identity theft and corporate fraud has escalated significantly. By 2026, the average cost of a data breach for a UK SME is projected to exceed £3.8 million when accounting for recovery, lost business, and forensic investigations. These costs often hit within the first 48 hours of an incident, draining cash flow when you need it most.
Trust is your most valuable asset. When clients discover their sensitive information is for sale on a forum, that trust evaporates instantly. Beyond the PR nightmare, the legal ramifications are severe. The Information Commissioner’s Office (ICO) continues to enforce UK GDPR with rigour. Fines can reach £17.5 million or 4% of annual global turnover, whichever is higher. For a growing business, these penalties represent a terminal threat rather than a mere operational hurdle.
Criminals use leaked data to craft hyper-personalised attacks. By understanding cyberattack risks from the dark web, you’ll see how a single leaked password allows a hacker to mimic your internal tone. They use this “insider knowledge” to fuel sophisticated phishing campaigns that bypass traditional filters. These attacks don’t look like spam; they look like a legitimate invoice from a known supplier or a direct request from your finance director.
Ransomware as a Service (RaaS)
The barrier to entry for cybercrime has vanished. Low-level criminals now rent sophisticated ransomware tools on a subscription basis for as little as £40 per month. We’ve seen a definitive shift toward “double extortion” tactics. It’s no longer enough to just lock your files. Hackers now steal your data first and threaten to leak it on the dark web unless a second ransom is paid. This makes a proactive managed IT support London strategy vital for your resilience. It’s about stopping the leak before the encryption even begins.
Identity Theft and Business Impersonation
Executive credentials are high-value targets. Once a CEO’s login is compromised, “CEO fraud” follows. Attackers send authorised-looking requests for bank transfers, often siphoning five-figure sums before the accounts team can verify the source. The loss of intellectual property to competitors via dark web leaks can strip away your hard-won market advantage in a single afternoon. There’s also a heavy psychological toll on your team. When staff realise their personal home addresses or bank details were exposed through a work breach, it creates a culture of anxiety that stifles productivity. Protecting your data protects your people.
Proactive Protection: Securing Your Business Infrastructure in Buckinghamshire
Reactive security is a relic of the past. In 2026, protecting your Buckinghamshire enterprise requires a shift toward “future-proofing” that anticipates threats before they manifest. We view security as a layered architecture; relying on a single firewall or antivirus tool is no longer sufficient when 82% of breaches involve a human element according to the latest industry data. Your London office needs a culture of security awareness where every staff member understands their role as a digital sentry. We don’t just install software; we build resilience into your organisational DNA.
Professional IT partners manage these complex risks behind the scenes, allowing you to focus on growth while we maintain your perimeter. By blending technical expertise with strategic foresight, we ensure that your digital assets remain secure regardless of how the threat landscape evolves. This layered approach creates multiple “fail-safes” that protect your data even if one individual link in the chain is compromised.
Implementing Dark Web Monitoring
Monitoring the dark web acts as a continuous, automated scan for compromised business credentials. It’s a vital early warning system that identifies leaked emails or passwords before a criminal can use them to infiltrate your network. If a staff member’s login appears on a leaker forum, we identify it immediately, allowing for a controlled password reset before a crisis occurs. We integrate this proactive monitoring directly into our managed IT services to ensure your protection is seamless and constant. This visibility transforms the dark web from a hidden threat into a manageable risk factor.
Essential Technical Safeguards
Multi-Factor Authentication (MFA) is the non-negotiable standard for 2026. Microsoft research indicates that MFA stops 99.9% of automated account takeover attacks. Beyond simple authentication, expert Microsoft 365 management serves as the primary line of defence for most SMEs in Hertfordshire. We configure your cloud environment to block suspicious logins from high-risk geographic regions and enforce strict data access policies to prevent internal leaks.
Resilience also depends on your recovery speed. We maintain regular, encrypted data backups stored in geographically separate, off-site locations. This ensures that even in the event of a sophisticated ransomware attack, your business remains operational without paying a penny to cybercriminals. Our approach focuses on three core pillars:
- Identity Protection: Ensuring only verified users access your sensitive data.
- Configuration Audits: Preventing “security drift” in your cloud applications.
- Immutable Backups: Creating data copies that cannot be altered or deleted by hackers.
Don’t wait for a breach to test your defences. Book a strategic security review with our team to future-proof your infrastructure.
Navigating a Breach: What to Do if Your Data is Discovered
Discovering your company’s sensitive credentials or intellectual property on the dark web is a high-pressure moment that requires a structured, logical response rather than panic. The first 24 hours are critical. Statistics from the 2024 Cyber Security Breaches Survey indicate that 31% of UK businesses face weekly attacks; those that recover fastest are the ones with a pre-defined incident response plan. Speed is your greatest asset. You must balance internal technical containment with external legal compliance to maintain your reputation and protect your bottom line.
Immediate Response Steps
You should immediately disconnect any compromised hardware from the network to prevent lateral movement by the threat actor. Once isolated, your team must initiate a forced password reset across the entire organisation. This process should include terminating all active user sessions to ensure stolen tokens or “remember me” cookies are invalidated. Finally, engage your IT support partner to conduct a forensic audit. This deep dive identifies the root cause of the leak, allowing you to close the vulnerability before the attacker returns. It’s about securing the perimeter and the core simultaneously to ensure the threat is fully neutralised.
Local Support and Reporting in the UK
Compliance is a legal necessity, not a choice. Under the UK GDPR, you must report a breach to the Information Commissioner’s Office (ICO) within 72 hours if it poses a risk to individuals. Failing to meet this window can lead to fines of up to £17.5 million or 4% of annual turnover. You should also report the incident to Action Fraud on 0300 123 2040 to obtain a crime reference number, which is often a requirement for your cyber insurance policy. The National Cyber Security Centre (NCSC) provides specific guidance for SMEs to help mitigate the impact of such events. Clear communication with your stakeholders is equally vital; drafting a transparent statement that outlines the steps taken to secure their data helps rebuild trust quickly.
Working with a local expert in London or Hertfordshire ensures your business isn’t just a ticket number in a global queue. A local partner can provide on-site support within hours, offering the hands-on resilience needed to restore operations. This proactive approach turns a potential disaster into a managed event, ensuring your business continuity remains intact. For comprehensive protection and recovery strategies, explore our tailored managed IT services designed for the local business landscape. We act as an extension of your team, providing the peace of mind that comes from professional, local oversight.
Future-Proof Your Business Resilience Today
The digital landscape for SMEs in London and Hertfordshire is shifting rapidly. By 2026, the speed of data exploitation means your company credentials could be traded on the dark web within seconds of a perimeter breach. Maintaining resilience requires more than basic antivirus software; it demands a comprehensive strategy that prioritises UK GDPR compliance and continuous infrastructure monitoring. You’ve seen how easily data migrates to the digital underworld and why proactive defence is the only way to protect your commercial reputation.
Digit-IT provides 20 years of experience supporting local firms, acting as a high-level strategic partner rather than a simple helpdesk. Our team delivers 24/7 threat detection and expert consultancy to ensure your operations remain seamless and secure. We bridge the gap between complex digital tools and your business goals, giving you the peace of mind to focus on growth. Don’t wait for a breach to reveal your vulnerabilities when a professional assessment can secure your assets today.
Secure your business with a professional IT audit from Digit-IT
We’re here to ensure your technology remains an advantage rather than a risk.
Frequently Asked Questions
Is it illegal to browse the dark web in the UK?
It’s entirely legal to browse the dark web in the UK using tools like the Tor browser. No specific law prohibits accessing these unindexed layers of the internet for research or privacy reasons. However, the Computer Misuse Act 1990 remains in full effect for any illicit activities conducted while connected. Since a 2024 study by King’s College London found that 57% of dark web sites host illegal content, we advise businesses to avoid casual browsing to mitigate unnecessary risk.
How can I tell if my business email is on the dark web?
You can identify if your credentials are compromised by performing a professional domain audit. These scans cross-reference your business emails against databases containing over 24 billion leaked records from historical breaches. We provide real-time monitoring that alerts your London team the moment a staff member’s details appear in a new data dump. This proactive visibility allows you to secure accounts before criminals can exploit them for 2026-style credential stuffing attacks.
Does a VPN protect me from the dark web?
A VPN provides a helpful layer of encryption but it won’t offer total protection from the threats found on the dark web. It effectively masks your IP address from your Internet Service Provider, yet it cannot stop a user from downloading malicious payloads or entering credentials into a phishing portal. We recommend a multi-layered security stack that combines encrypted tunnels with advanced endpoint detection. This approach ensures your Hertfordshire office remains resilient against sophisticated digital incursions.
What is the difference between the deep web and the dark web?
The deep web refers to any part of the internet not indexed by search engines, such as your private banking portal or internal HR systems. It accounts for roughly 90% of all online content and is essential for standard business operations. The dark web is a much smaller, intentional subset that requires specific configuration and software to access. While the deep web keeps your data private, the dark web is frequently used as a marketplace for trading stolen corporate assets.
How much does dark web monitoring cost for a small business?
Dark web monitoring for a small business in the UK typically costs between £40 and £150 per month. This price varies based on the number of employee identities you need to track and the depth of the forensic reporting provided. Investing in this service is a strategic move, especially when compared to the £3.4 million average cost of a UK data breach reported in 2024. Our bespoke packages integrate this oversight into your wider IT strategy to ensure seamless protection.
What should I do if my password is found in a dark web leak?
You must change the compromised password immediately and update any other accounts where that password was reused. This prevents a single leak from triggering a cascade of breaches across your entire business infrastructure. You should also enable Multi-Factor Authentication (MFA) on every possible application to create a secondary barrier. Since 81% of hacking-related breaches involve stolen credentials, taking these steps is vital for future-proofing your organisation against unauthorised access.
Can the dark web be shut down by the police?
Law enforcement agencies cannot shut down the dark web because it’s a decentralised network with no central server. While the National Crime Agency and FBI successfully seized the LockBit ransomware site in February 2024, new nodes and marketplaces often emerge to take their place. Because the network is designed to be resilient, you can’t rely on global policing for your security. Your business must take ownership of its digital borders through constant monitoring and robust defensive protocols.
How often should my business conduct a dark web scan?
Your business should move away from manual checks and implement continuous, 24/7 dark web monitoring. Since a new cyber attack occurs every 39 seconds globally, an annual or quarterly scan leaves a significant window of vulnerability for your Hertfordshire firm. Our automated systems provide instant notifications the moment your data is detected in a breach. This steady, methodical oversight ensures you can react to threats in seconds, maintaining the peace of mind and business continuity you require.